Information security has always been important across organizations in all industries. The challenge is that managing cybersecurity risks has become increasingly difficult. This is due to the growing complexity of IT environments, the rise in sophisticated threats and an increased reliance on cloud services, all of which create more potential entry points for attackers. However, you can use a risk assessment framework to spot your biggest potential threats.
| “Understanding your organization’s potential attack surface is your first step towards a strong risk mitigation strategy.” – Jason Sondhi, CEO, EXOS IT |
A standardized technology risk management framework ensures that risk assessments are conducted consistently across all departments and projects. This consistency improves the reliability of risk evaluations and enables repeatable processes that streamline ongoing assessments.
While there are some general best practices that all organizations should follow, such as the National Institute of Standards and Technology (NIST) Risk Management Framework (RMF), how you should prioritize risks may be more elusive. Your security risks may vary based on your industry and operational model.
This article will provide some instructions on how you can reveal these risks. We will also provide suggestions on how you can use these insights to craft your own customized risk assessment framework.
How to Identify Your Organization’s Biggest Cybersecurity Risks
Conduct a Comprehensive Asset Inventory
Compile a detailed list of hardware, software, data repositories and network components. Prioritize assets based on their importance to operations and the potential impact of a security breach. Knowing what you need to protect is essential for targeted risk mitigation.
Engage Key Stakeholders Across Departments
Collaborate with leaders from various departments, such as finance, HR and legal, to uncover risks beyond IT. These stakeholders can provide insight into operational dependencies and data privacy concerns. Their input ensures a comprehensive risk assessment that aligns with organizational goals.
Choose a Cybersecurity Partner with a 97% RatingChoose EXOS IT |
Evaluate Third-Party Risks
Assess the cybersecurity posture of vendors, contractors and partners who have access to your systems or data. Third-party relationships can introduce vulnerabilities if not properly managed. Regular audits and strict access controls help mitigate this risk, so be sure to include these evaluations as part of your risk assessment criteria.
Review Past Security Incidents
If your organization has ever dealt with past incidents, review what happened and what was done to resolve the issue. An “incident” is not necessarily a catastrophic event. You should also include failed attack attempts as opportunities to gain insights into how you can protect your IT systems.
Prioritize Risks Based on Impact and Likelihood
Use a structured approach, such as a risk matrix, to evaluate each identified threat. Focus on those with a high likelihood of occurrence and significant potential impact on operations. Prioritizing risks ensures resources are allocated effectively.
Please observe the quadrants below to see how you should deal with threats based on impact and likelihood.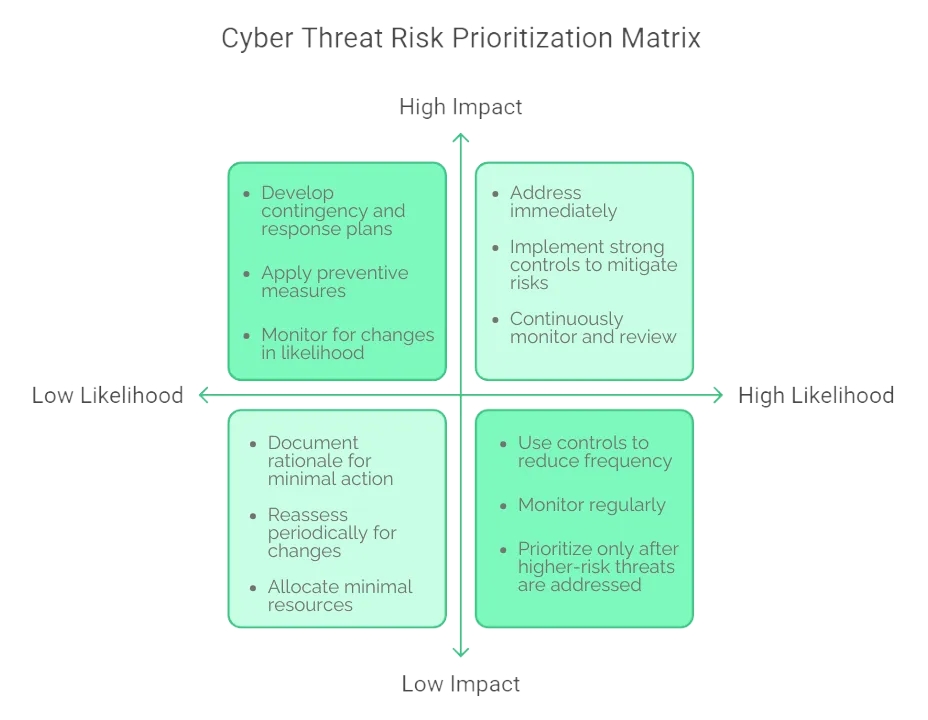
How to Tailor Your IT Risk Assessment Framework to Your Organization
Define Your Organization’s Risk Appetite
Establish clear boundaries for how much risk your organization is willing to accept. This guides decision-making and helps prioritize mitigation efforts. Without a defined risk appetite, resources may be misallocated to less critical threats.
Integrate Insights from Initial Assessment
Leverage the risks discovered in your initial assessment to focus your framework on the most pressing threats. For example, if third-party vulnerabilities are significant, strengthen vendor management processes. Tailoring your framework to address known risks improves its effectiveness.
| Explore More of Our Leading Insights |
Map Business Processes to IT Infrastructure
Identify which systems support critical operations and how they interconnect. This mapping helps prioritize risks that could disrupt essential services. Understanding these relationships ensures that mitigation efforts target the most vital assets.
Here are some examples of the types of interconnections that you should watch out for.
| Business Process | Supporting IT Systems | Interconnections | Risk Mitigation Focus |
| Customer Service Operations | CRM platforms, VoIP systems | Integrated with email servers and databases | Minimize downtime of communication tools |
| Financial Transactions | Accounting software, payment gateways | Connected to secure servers and audit logs | Protect data integrity and transaction continuity |
| Supply Chain Management | Inventory systems, vendor portals | Linked to ERP solutions and logistics platforms | Reduce disruption in supply chain data flow |
| Human Resources Management | HRIS platforms, employee portals | Connected with internal databases and payroll systems | Secure employee data and payroll processing information |
| Sales and Marketing Activities | Marketing automation, sales tracking software | Integrated with CRM and analytics tools | Maintain continuity of lead and customer tracking |
Develop a Detailed Mitigation and Response Plan
Create a structured plan outlining how identified risks will be addressed, including specific actions, responsible parties and timelines. Incorporate scenarios based on the most likely and impactful threats. A detailed plan facilitates swift response and minimizes potential damage. Be sure to document this plan so that anyone at your organization can use it for reference.
Establish Continuous Improvement Processes
Schedule periodic reviews and incorporate feedback from more recent incidents or changes in technology. Continuous improvement helps your organization maintain an up-to-date and effective risk management strategy.
| Explore Other Leading Cybersecurity Services From EXOS IT | ||||
| 24×7 Monitoring | EDR | Dark Web Monitoring | DNS Filtering | Vulnerability Scanning |
Ask the Experts About Your IT Risk Analysis Framework
CloudSecureTech discusses how 60% of organizations are investing in new technology to enhance their risk management processes. While this desire is understandable, there is the possibility that you may choose the wrong technology tools for your needs. 79% of organizations find it challenging to procure new technology despite increased investments.
EXOS IT can help you overcome that challenge and invest wisely. We can work with you to help you establish an effective IT risk assessment framework and guide you towards the best technology tools to implement it. We will also continue to work with you post-implementation to answer any questions you may have.
Reach out today to get started.




